Security & Encryption
Security by design, not by promise
Securoo is built on true end-to-end encryption and a strict zero-knowledge model. Your files are encrypted on your device, with keys only you control — so no one, including Securoo, can read your data.

Your data is encrypted before it leaves your device.
With Securoo, encryption happens directly in your browser or mobile app. Files and messages are encrypted before they are uploaded, and can only be decrypted by keys you own.
Security that protects you from breaches and fines.
End-to-end encryption gives you the highest level of protection for your clients’ documents and identity data. Even if someone gained access to our infrastructure, all they would find is encrypted noise. Strong protection against data breaches and insider threats.
Minimizes the impact of ransomware and credential theft.
Helps you meet and exceed GDPR requirements, reducing the risk of fines up to €20 million.


Every user gets a secure login and their own master key.
When someone joins Securoo, we create a secure, salted and hashed login plus a unique master key derived from their credentials. On top of that, Securoo generates an individual RSA 4096-bit key pair for each user.
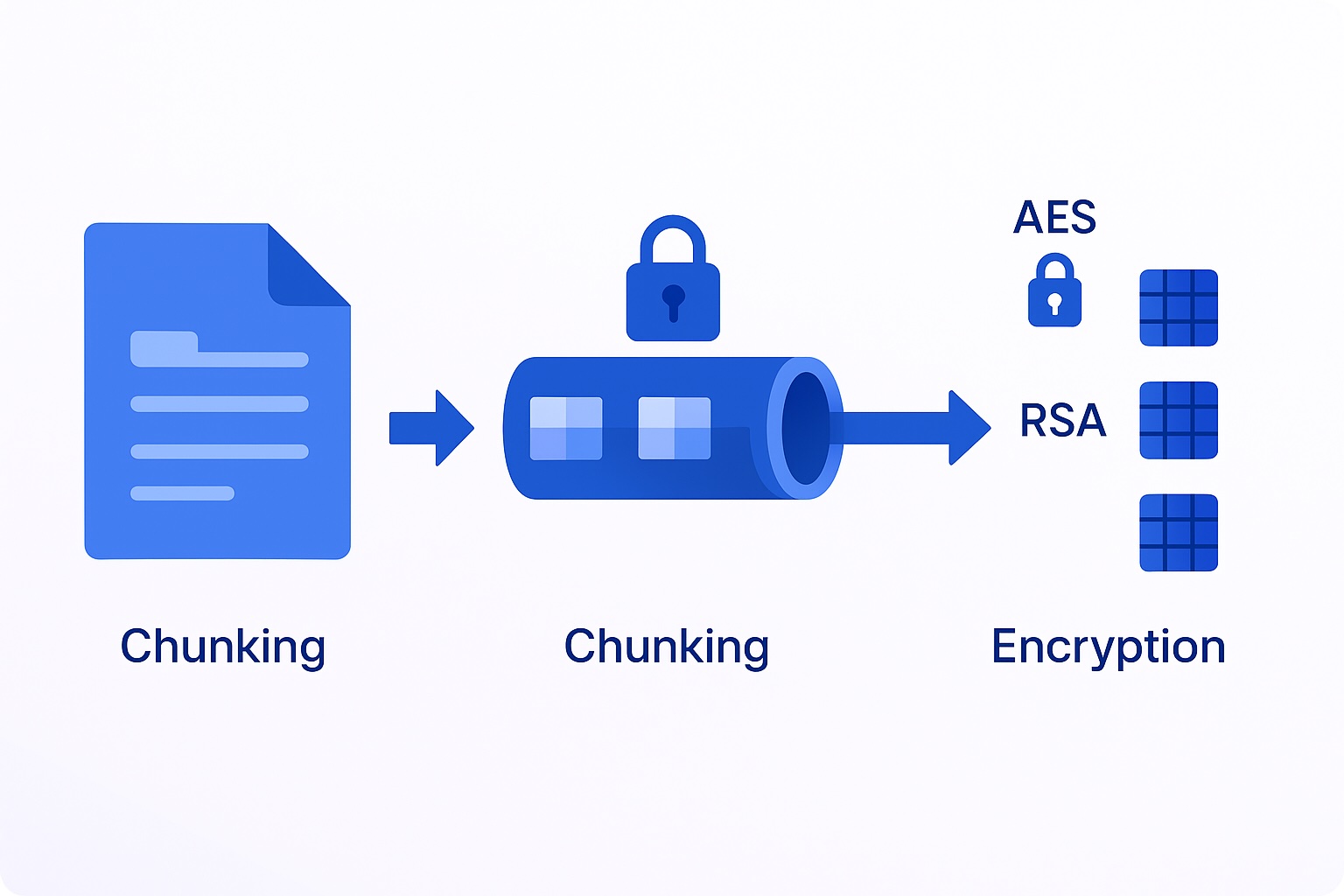
Files are chunked, encrypted, and sent as unreadable fragments.
Every time you upload a file, Securoo applies a multi-layer encryption process that takes place entirely on your device.

A mnemonic Recovery Key only you control.
When you activate Securoo Business, we generate a mnemonic Recovery Key that allows you to recover your encrypted data if you ever lose access to your main login.
Penetration Testing Report
Independent security testing by certified professionals.
Securoo undergoes regular penetration testing conducted by Cyberglobal, an external CREST-aligned cybersecurity firm.
These tests validate the security, resilience, and integrity of our platform against real-world attack scenarios.
You can require us the latest reports to review the results of our periodic security assessments and the continuous improvements we apply to protect your data.
Whitepaper Document
Encryption & Architecture Whitepaper
Ask for our official whitepaper to understand how Securoo protects sensitive data through zero-knowledge architecture, client-side encryption, RSA-4096 key management, secure file chunking, and recovery mechanisms.
The document provides a detailed technical explanation of our security model, encryption flow, and the cryptographic choices behind our platform.
Need a quick help or have questions?
W&B Asset Studio SL
Edificio Europe
Avenida Aragon 30 - PL.8
46021 Valencia
wbstudio.tech
Securoo is a product of W&B Asset Studio SL
©2025 WB Asset Studio SL
– All rights reserved
